As our Power Mac G5s and other PowerPC Macs age rapidly, our machines are trapped in time. We can count on one hand, maybe two, the amount of software packages that are still being actively maintained and updated for our hardware, including the valuable TenFourFox. Of course, it’s not the end of the world to use dated but perfectly functional software to write our papers, design websites, create graphics, and so on, but getting our PowerPC Macs online in a secure and functional way with the complexity of the modern web gets trickier each year.
Don’t forget that Leopard (Mac OS X 10.5) received its last security update… a long time ago.
Wouldn’t it be nice to tinker with modern up to date software in a more secure operating system?
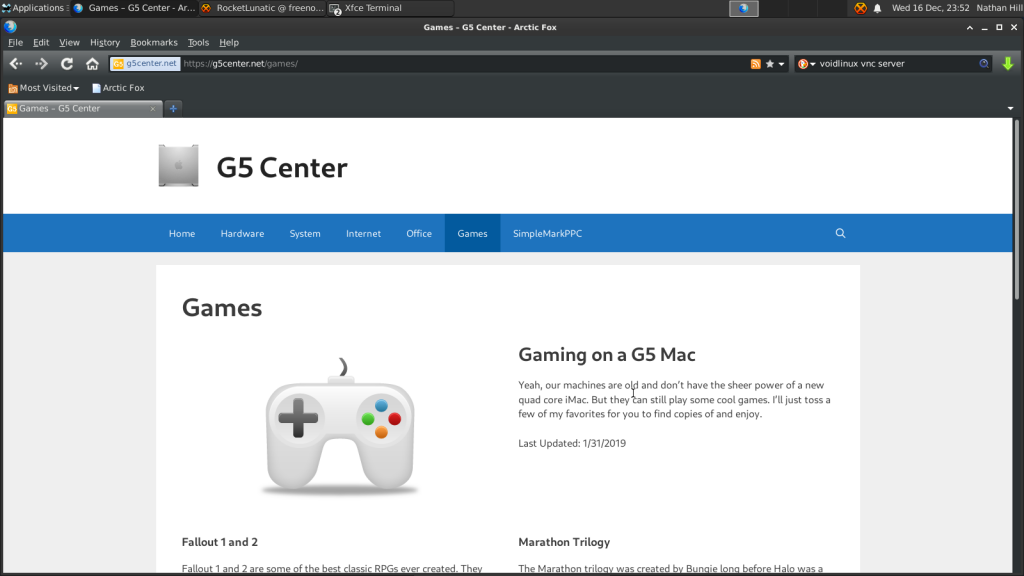
Say hello to Void Linux for PPC, pictured above running on my Mac Mini G4.
What is Void Linux?
Void Linux PPC is an up to date, community-led Linux-based OS. The distribution is not official but driven by a dedicated group of developers using Void Linux as its base. The main target and energy around the distribution focuses on newer PowerPC machines, including Raptor’s Blackbird line of motherboards and machines, but our older PowerPC Macs are supported, including install instructions and well-organized tips and tricks to get started.
In the larger picture, Void Linux stands out due to its own package management system called xbps, and per the main distribution website, it emphasizes stability over a rolling release. However, packages are frequently updated. For example, when the newest XFCE4 desktop environment was released on December 22, I was able to update to the latest and greatest XFCE4 as of January 1. The most recent kernel version is 5.9.16_1, which is so cool to run recent Linux kernels on such old hardware.
As I highlighted in my brief look at MacBuntu several weeks back, you can make a strong argument that older machines should stick with software from its period just for speed alone, but it is cool to be able to use more recent Linux kernels, desktop environments, and other open source applications on your ancient Mac. Performance, while not blazing fast, is quite solid.
Another area that makes Void Linux unique is that it supports both musl and gnu libc implementations of the standard shared Linux library. These are the libraries that serve as the common foundation for many core Linux software packages across various distributions. MUSL is intriguing for PowerPC users because it is newer and “cleaner”, but gnu libc is more popular and benefits from years of optimization. There is one other added bonus – libc works better with some hardware drivers, especially proprietary gpu drivers. I ended up going with the libc version as it avoids a couple of GPU bugs on my ancient Radeon 9200 GPU in the Mac Mini. You can read about GPU compatibility with Void Linux PPC on this handy chart.
The PowerPC distribution also has a quite thorough number of software packages available for install, though it appears that the number fluctuates as some package updates require fixes to be able to build properly on our old Macs. I know there were a few software packages I couldn’t find during my test run, but most things I needed are available in one form or another. You can poke through the list of available packages here.
What is the install like?
Install was relatively straightforward. Using a USB flash drive, as my old DVD drive in the G4 died years ago, I booted into a basic Void Linux PPC environment, typed in void-installer, and made my way through the process. The website offers an excellent step by step tutorial, including tips to make sure your hard drive is properly formatted, even in the case where you might want to still be able to boot into Mac OS X. My first major issue during installation was getting my internal SSD to partition and format. No matter what I tried, my partition map came out all wrong. I ended up flashing the install image to the USB drive a second time. For whatever reason, it worked. No idea why. (Hint: Be ready for these kinds of strange experiences with Linux from time to time.)
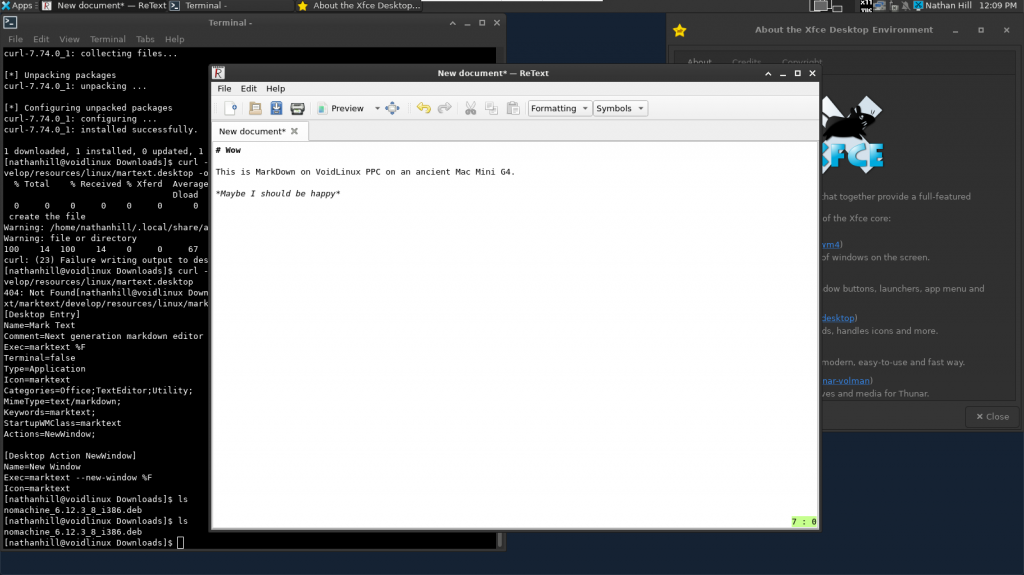
After the install, you are greeted with a login prompt, which is perfect if you want to run your Mac Mini as a server. Then you can begin updating the package manager and core packages using xbps-install -Su and building the environment you are comfortable with. Various desktop environments and window managers are available. I prefer XFCE4 for its flexibility, style, and ability to get out of the way. Plus, it’s pretty light. There are lighter and beefier options available though.
The install was the first part of the process – what can be time consuming and head scratching is that next step of hunting for software packages that will fill your needs. I have experience with other distributions, so it was a little frustrating to have to hunt for the right package name since it could be named differently in Void Linux. Nonetheless, with patience and a few google searches, I was able to begin building the environment you see above. Sure, there were bugs along the way, like how sudo xbps-install xfce4 didn’t include all the packages I really needed. Luckily, fellow users in the voidlinuxppc channel on Freenode were able to help. Great people!
How is it on the internet?
Unfortunately, web browsing is a slight challenge.
One webkit-based browser available on Void Linux PPC is Epiphany, though you will need to type in an EXPORT command listed in the Frequently Asked Questions page to make sure it renders webpages the correct way. For me, it lags and wasn’t very reliable.
I was able to install the ArcticFox PowerPC Debian package with minimal fuss, and it works great. However, Arctic Fox is an older build.
Of course, you can also use some command line web browsers as a backup plan.
As some good news, I recommend following the work of Jake Hamby who is seeking to build more recent versions of FireFox for PowerPC Linux. May his efforts bear fruit soon!
Beyond web browsing, you can easily ssh into your favorite servers, download multiple IRC clients, and use your Mac as a server. I am accessing it over x11vnc too, and the performance is decent on my personal network. The nice thing is that I know security updates are constantly on the way for both internet facing applications as well as the core software in the distribution. That’s really cool.
Could it be a daily driver?
Sure. Some apps are just as speedy and functional, if not as pretty, as many Mac OS X Leopard variants. For example, I’ve switched from XChat to Quassel for my preferred IRC client. Both options work great. LibreOffice should be available, though I’ve installed AbiWord for now since it is lighter and I’ve never been a fan of LibreOffice. Another app that seems promising for coding and text work is Geany. A workable Markdown editor is ReText, though I wish some newer and better looking options were available.
And really, I’ve just started scratching the surface of resources of available packages for install.
For developers on these old machines, you’ve got a variety of options to tinker with, including Python3.
Best of all, you can configure Void Linux PPC to your liking. XFCE4 in particular can be made to look very Mac-like, and there are a plethora of themes available to give you dark, vintage, or minimal styles.
But what are its downsides?
In addition to some general frustrations and a learning curve that could scare off some users, Void Linux PPC has the same challenges that all Linux distributions face – hit or miss hardware support, lack of polish, software that can be functional but look like crap, lots of error messages that require googling to figure out how to address, and a general non-user friendliness.
You will definitely miss some of your favorite software packages from the Mac world.
Mac OS X is simply beautiful and optimized for our Macs. Going to Linux, where most of the desktop environment has to run without any hardware optimization, is jarring. I think Linux could be better optimized, but who is going to hire developers to target hardware as old as ours? There are plenty of cases where new PC hardware doesn’t run well in Linux. It’s simply the nature of open source software. People spend time focusing on what they are passionate about, hardware support requires buy in from hardware manufacturers, and these old PowerPC machines are only on a few people’s radars anymore.
Case in point, I spent a few hours working to get a compositor going with XFCE4. The default compositor should be turned off immediately for a little better performance, relying on software rendering rather than hardware rendering. Another option is the venerable compiz compositor, but though it is available in the repositories, enabling it means an instant freeze and hardware crash. It would be nice to have even a minimal compositor to get better performance out of window draws and refreshes for a more pleasant desktop experience. (Maybe a dash of transparency wouldn’t hurt.)
The other challenge is your need to search Google frequently or reach out for help to sort through bugs that really shouldn’t exist. On one hand, some of these bugs are ignorable. For example, I received a constant PolicyKit error when launching XFCE4 for a while, until I found the other dependencies XFCE4 was looking for, including a window manager to load on launch. The error didn’t affect the operation of XFCE in a show stopper way – just annoying. XFCE’s included Power Manager didn’t work as well, exiting with an error, until I installed some other missing components. Fixing these issues wasn’t intuitive, since the PolicyKit error or PowerManager error tell you nothing about next steps.
Part of this comes from the design of Linux to have the ability to install just what you need. For a server or a secure environment, that makes sense, but for desktop environments, why not install every component, even alternative components like themes, to save the user time and insure a smooth experience? Just because the component is installed, it doesn’t mean the user will have to configure it or even run it. And while I can hear the argument that learning to tinker and solve problems is a win, it’s not really. I don’t think I will have any other moment in my life when I need to know how to fix PolicyKit errors in Linux.
Just be ready when entering the world of Linux to know that there will be issues, and you will need to take some time to get the optimal environment/setup that works for you. Do your best not to give up, and keep in mind you can always start over.
Conclusion
Ultimately, I like Void Linux PPC and recommend it for PowerPC users who want to move to an operating system that is still getting software updates. Since I already have Leopard going on my Power Mac G5, I’m excited to continue to tinker with my Mac Mini G4 and see what I can do with it. I found the documentation on the website as well as the MacRumors thread and VoidLinuxPPC IRC channel helpful resources to learn more and get feedback. That’s a good sign.
There are challenges – you will need to be prepared to roll up your sleeves and do some proactive tinkering to get things fully working. Linux may not be for you, and that’s okay. But it is a great option to keep our PowerPC machines rolling into the void of uncertainty that is 2021 and beyond.
— Nathan

